Certified Ethical Hacker (CEH): CEH-001
Want to pass your Certified Ethical Hacker (CEH) CEH-001 exam in the very first attempt? Try Pass2lead! It is equally effective for both starters and IT professionals.
- Vendor: GAQM
- Exam Code: CEH-001
- Exam Name: Certified Ethical Hacker (CEH)
- Certifications: GAQM Certifications
- Total Questions: 878 Q&As
- Updated on: Mar 03, 2025
- Note: Product instant download. Please sign in and click My account to download your product.

- Q&As Identical to the VCE Product
- Windows, Mac, Linux, Mobile Phone
- Printable PDF without Watermark
- Instant Download Access
- Download Free PDF Demo
- Includes 365 Days of Free Updates

VCE
- Q&As Identical to the PDF Product
- Windows Only
- Simulates a Real Exam Environment
- Review Test History and Performance
- Instant Download Access
- Includes 365 Days of Free Updates
Passing Certification Exams Made Easy
Everything you need prepare and quickly pass the tough certification exams the first time
- 99.5% pass rate
- 7 Years experience
- 7000+ IT Exam Q&As
- 70000+ satisfied customers
- 365 days Free Update
- 3 days of preparation before your test
- 100% Safe shopping experience
- 24/7 Support
GAQM CEH-001 Last Month Results
Free CEH-001 Exam Questions in PDF Format
Related GAQM Certifications Exams
CEH-001 Online Practice Questions and Answers
Questions 1
You went to great lengths to install all the necessary technologies to prevent hacking attacks, such as expensive firewalls, antivirus software, anti-spam systems and intrusion detection/prevention tools in your company's network. You have configured the most secure policies and tightened every device on your network. You are confident that hackers will never be able to gain access to your network with complex security system in place. Your peer, Peter Smith who works at the same department disagrees with you. He says even the best network security technologies cannot prevent hackers gaining access to the network because of presence of "weakest link" in the security chain. What is Peter Smith talking about?
A. Untrained staff or ignorant computer users who inadvertently become the weakest link in your security chain
B. "zero-day" exploits are the weakest link in the security chain since the IDS will not be able to detect these attacks
C. "Polymorphic viruses" are the weakest link in the security chain since the Anti-Virus scanners will not be able to detect these attacks
D. Continuous Spam e-mails cannot be blocked by your security system since spammers use different techniques to bypass the filters in your gateway
Questions 2
What type of port scan is shown below?
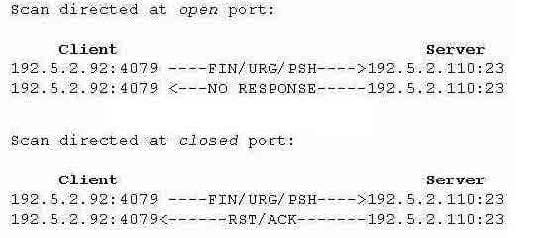
A. Idle Scan
B. Windows Scan
C. XMAS Scan
D. SYN Stealth Scan
Questions 3
LM authentication is not as strong as Windows NT authentication so you may want to disable its use, because an attacker eavesdropping on network traffic will attack the weaker protocol. A successful attack can compromise the user's password. How do you disable LM authentication in Windows XP?
A. Stop the LM service in Windows XP
B. Disable LSASS service in Windows XP
C. Disable LM authentication in the registry
D. Download and install LMSHUT.EXE tool from Microsoft website
Reviews
-
So happy. I passed the exam with the help of this material. Good luck to you.
-
passed the exam today. all the question from this dumps,so you can trust on it.
-
Thanks for the help of this dumps, i achieved the full score in the exam. I will share this dumps with my good friends.
-
This dumps was introduced by my good friend several month ago. At first, I don't think it will help me a lot. But when I found many new questions that I never found from other study materials, i begun to pay more attention on this dumps. At last, I only used this dumps for preparing my exam. A moment ago, i have cleared that i passed the exam with almost full score. Thanks for this dumps, i will recommend to others just as my friend do.
-
Already pass. Valid dumps. Good site. Thanks guys.
-
i have passed today, All the questions are from their dumps, thanks for this dumps.
-
Answers are correct. Questions are valid.Recommend strongly.
-
Valid dumps. I hope all my friend will pass the exam, so I will introduce this dumps to them.Good luck to them and you.
-
I knew this dumps by accident. One month ago, I searched on the Internet and found this material. At first, I didn't dare to pay much attention on this material and also brought many other material. But when i used all the materials I brought , I found that there are many new questions and the answers are or accurate in this material.Gradually,I payed more attention on this material and at last I only used this material. Today I have cleared that I passed the exam with high score. So I recommend this material strongly.
-
I just passed my exam by using this dumps, thanks to thier efforts which help to get the certificates in easy way.

 Printable PDF
Printable PDF