9L0-415 Online Practice Questions and Answers
Questions 4
You have a user account on an OS X Mountain Lion computer that has multiple user accounts. How can you interact with another user's Dropbox folder that has default permissions?
A. You can see its contents, but you cannot add files to it.
B. You can neither see its contents nor add files to it.
C. You cannot see its contents, but you can add files to it.
D. You can see its contents and you can add files to it.
Questions 5
You have a Mac OS X v10.6.8 computer that has several user accounts. If you install OS X Mountain Lion without first erasing the target volume, what will happen to the 10.6.8 operating system and the existing user accounts?
A. The Installer archives the 10.6.8 OS and installs Mountain Lion. It maintains the user accounts.
B. The Installer upgrades the 10.6.8 OS to Mountain Lion. It maintains the user accounts.
C. The Installer replaces the 10.6.8 OS with Mountain Lion. It archives the user accounts, but they can be restored manually.
D. The Installer erases the 10.6.8 OS and installs Mountain Lion. It archives the user accounts, but they can be restored manually.
Questions 6
You upgrade a Snow Leopard Mac that has legacy FileVault encryption to Mountain Lion. If a user forgets his login password, how can you help him regain access to his encrypted home folder?
A. Log in to the admin user account, open Keychain Access, open the user's login keychain, and then let the user view the account password.
B. At the Login Window, enter an incorrect password three times in a row. When the "forgot your password" dialog appears, click the Arrow next to Master Password. Enter the master password, and then reset the user account password.
C. Log in to the admin user account, open Users and Groups preferences, click Reset Password, enter the admin password, and then reset the user account password.
D. At the Login Window, enter an incorrect password three times in a row. When the "forgot your password" dialog appears, click the Arrow next to Apple ID. Enter the user's Apple ID, and then reset the user account password.
Questions 7
Review the screenshot and answer the question below.
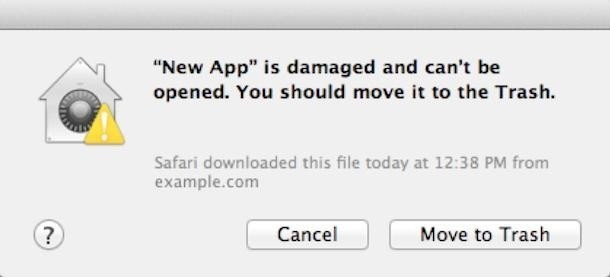
You downloaded an app using Safari. When you try to open the app, you see the message shown above. What is a possible explanation?
A. The sandbox into which the app was downloaded by the quarantine system has become corrupted.
B. The certificate needed to decrypt this app cannot be found in the keychain.
C. Gatekeeper has recognized that the app was altered after it was signed.
D. The app was signed using a certificate from an unknown authority.
Questions 8
The minimum requirements for upgrading OS X Mavericks are:
OS X v10.6.8 or later 2 GB of memory 8 GB of available space Some features require an Apple ID Some features require a compatible Internet service provider Compatible Mac model (as listed on www.apple.com/osx/specs/)
A. What are the minimum hardware requirements for upgrading a system with OS X Mavericks?
B. What are the system requirements for using FileVault 2?
C. What two volume formats are supported for an OS X system volume?
D. What are the requirements for purchasing applications via the Mac App Store?
Questions 9
What are PPD files responsible for?
A. PostScript Printer Description (PPD) files are printer driver files that instruct the CUPS system on how to communicate with specific printer models.
B. If a client sharing service is compromised, an unauthorized user can control your Mac and execute unwanted applications or processes.
C. The Finder hides traditional UNIX resources from average users because they don't need to have access to those items. If users need access to these UNIX items, they can access them from Terminal.
D. Common UNIX Printing System (CUPS) manages all printing for OS X, including both local and shared printing.
Questions 10
Why would you want to open an application in 32-bit mode?
A. Documents saved to iCloud can be managed from the application that was used to create and save the document. iCloud documents don't appear anywhere in the Finder that a user would normally look.
B. Using the Finder Info window you can force an application to open in 32-bit mode. This step is necessary for a 64-bit application to support older 32-bit plug-ins or application resources.
C. The master password is used to reset local account passwords.
D. The OS X Mavericks installer can be downloaded from the Mac App Store for free.
Questions 11
The Privacy pane of Security and Privacy preferences can be used to allow or disallow applications' access to Location Services, Contacts, Calendars, Reminders, social network services, and Accessibility application access.
A. How can you acquire the OS X Mavericks installer?
B. How can you limit the use of Location Services?
C. How can you identify duplicate fonts?
D. What does the master password do?
Questions 12
How is the Domain Name Service (DNS) used to facilitate network naming?
A. The OS X Mavericks installer can be downloaded from the Mac App Store for free.
B. Keychains are used to store secrets such as resource passwords, digital certificates, and encryption keys. The keychain system can also securely store Safari AutoFill information, Internet Account settings, and secure text notes.
C. The Archive option in the Finder creates compressed zip archive files.
D. The DNS service is used to translate host names to IP addresses via forward lookups and translate IP addresses to host names via reverse lookups. DNS is architected as a hierarchy of worldwide domain servers. Local DNS servers provide name resolution and possibly host names for local clients. These local DNS servers connect to DNS servers higher in the DNS hierarchy to resolve both unknown host names and host local domain names.
Questions 13
How can you limit a user account from having full access to all applications?
A. Parental Controls can further limit a user account. Examples include enforcing a simple Finder, limiting applications and widgets, limiting Mac App Store content, setting time limits, and content filtering for several applications included in OS X.
B. The Archive option in the Finder creates compressed zip archive files.
C. Resource contention occurs when fast user switching is enabled and a user tries to access an item another user already has open in the background. Document contention occurs when a user attempts to open a document another user has already opened. Peripheral contention occurs when a user attempts to access a peripheral already in use by another user's open application. Application contention occurs when the second user attempts to access an application designed to run only once on a system.
D. By default on OS X, opens Archive Utility, the default application for opening zip archive files. Archive Utility, expands the contents of the zip archive next to the same location as the original zip archive.
