352-001 Online Practice Questions and Answers
Questions 4
Refer to the exhibit.
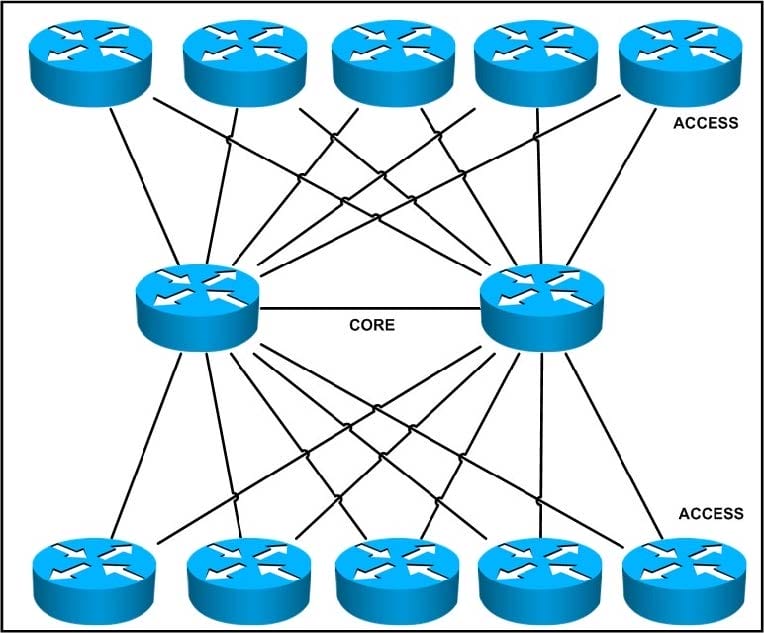
What limitations exist in this design, given that the access layer devices are expected to steadily increase by two devices per week for the next year?
A. scalability
B. serviceability
C. redundancy
D. resiliency
Questions 5
A network design shows two routers directly connected to an Ethernet switch using optical connections. There is an OSPF adjacency between the routers. In this design, which solution will ensure that interface down detection is reported as quickly as possible to the IGP?
A. optimized OSPF SPF timers
B. Bidirectional Forwarding Detection
C. automatic protection switching
D. optimized OSPF LSA timers
E. Ethernet OAM CFM monitoring
Questions 6
You are a network designer and are responsible for ensuring that the network you design is secure. How do you plan to prevent infected devices on your network from sourcing random DDoS attacks using forged source addresses?
A. ACL-based forwarding
B. ACL filtering by destination
C. Unicast RPF loose mode
D. Unicast RPF strict mode
Questions 7
Why should IGP advertisements be disabled on an access link where a host is attached?
A. because hosts do not run routing protocols
B. to prevent the injection of bad routes
C. to reduce router overhead
D. because edge hosts are statically routed
Questions 8
To meet specific business requirements, QoS-marked traffic must be sent over a dedicated link.
Which technology fulfills this requirement?
A. MPLS
B. Q-in-Q tunneling
C. policy-based routing
D. EIGRP with modified metrics
Questions 9
Refer to the exhibit.
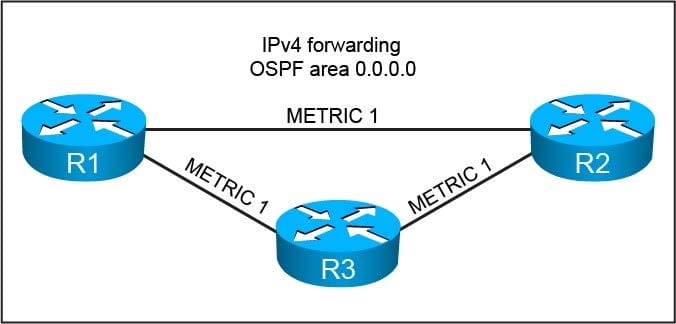
You are asked to design this OSPF network to converge within 60 ms for unicast packets after a topology change due to a single link failure. Which technology can be enabled while conforming to the design requirements?
A. Loop-Free Alternates
B. BFD
C. IGP neighbor timer tuning
D. IGP SPF timer tuning
E. RSVP-TE Fast Reroute
Questions 10
Which three reasons to deploy an IDS sensor in promiscuous mode when you design a security solution are true? (Choose three.)
A. Solution should be resistant to sensor failure.
B. Solution should allow for stream normalization.
C. Solution should not impact jitter and latency for voice traffic.
D. Solution should allow for signature-based pattern matching.
E. Solution should allow to deny packets inline.
Questions 11
For the following items, which one is the weakness of rate limiting as a response to a DoS attack?
A. Rate limiting does not drop enough packets.
B. Rate limiting does not detect attacks.
C. Rate limiting only works on inbound traffic.
D. Rate limiting is too processor-intensive.
Questions 12
Refer to the exhibit.
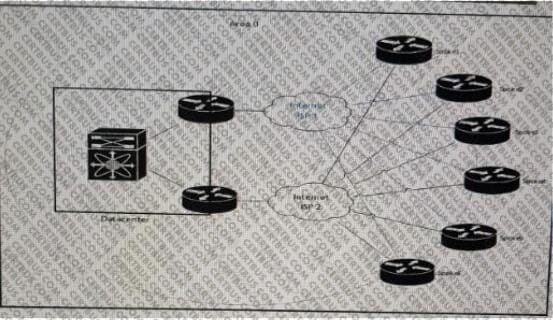
You must review this single OSPF area, DMVPN network because the company has noticed a few area 0 convergence and stability issues. Also, traffic destined to the data center from one of the spokes as the next hop on the path. The
company prefers that all traffic destined to the data center uses the least amount of hops.
Which solution resolves these issues with the minimum amount of changes on the network?
A. Migrate from OSPF to static routes between the hub routers and the spoke routers and deploy IP SLA for route health checks
B. Migrate from OSPF to EIGRP between the hub routers and the spoke routers
C. Modify OSPF cost metrics on all backup links
D. Create areas between each hub and their spoke routers, to ensure that the hub routers become DRs
Questions 13
Refer to the exhibit.
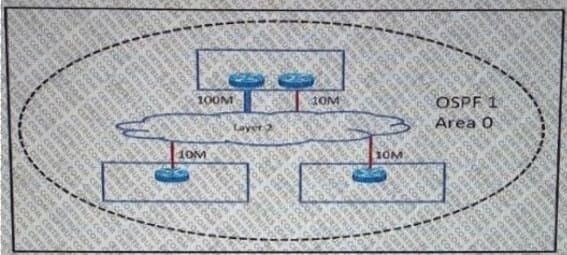
An enterprise has three sites over a Layer 2 Metro Ethernet ELAN service. 100Mb/s and 10 Mb/s links have been provisioned to provide redundancy for the head office. When OSPF routing enabled to provide connectivity and the correct bandwidth statement has been applied to each interface, the branch sites observe two equal-cost routes to the head office. The enterprise wants to send all traffic through the 100 Mb/s link and use the 10Mb/S link strictly as a backup. Which OSPF network type must be set to ensure that the head office 100 Mb/s circuit is preferred over the 10 Mb/s circuit, at the same time minimize the amount of configuration required on all of the routers throughout the network?
A. NBMA
B. Point-to-multipoint
C. Point-to-point
D. Broadcast
